Category: Darkweb Developer
Endgame V3: The Ultimate Anti-DDoS Solution for the Darknet
“Endgame V3: The Ultimate Anti-DDoS Solution for the Darknet” Introduction: In the realm of the Darknet, where security and anonymity…
Endgame V3: Revolutionizing Darknet Security with Unprecedented Anti-DDoS Capabilities
Endgame V3: Revolutionizing Darknet Security with Unprecedented Anti-DDoS Capabilities Introduction: In the hidden depths of the Darknet, where security…
Exploring the Differences and Improvements in EndGame V3: A Powerful Onion Service DDoS Prevention Front System
Title: Exploring the Differences and Improvements in EndGame V3: A Powerful Onion Service DDoS Prevention Front System Introduction: In the…
Understanding 12P: The Twelve Principles for Effective Project Management
Title: Understanding 12P: The Twelve Principles for Effective Project Management Introduction: Project management is a complex and multifaceted discipline that…
Exploring Anonymity Networks: A Comparative Analysis of I2P and Tor
I2P (Invisible Internet Project) and Tor (The Onion Router) are both anonymity networks that aim to provide privacy and security…
How to setup I2P on onion site
Setting up an Onion Site on I2P I2P, also known as the Invisible Internet Project, is an anonymous overlay network…
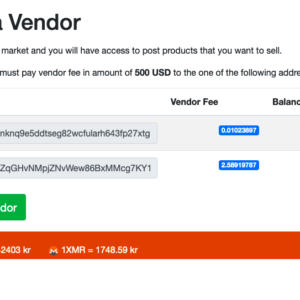
Complete Guide: Installing Monero Core Node with JSON-RPC on Ubuntu
To install a Monero core node on Ubuntu and enable JSON-RPC, you can follow the steps below: Update your system:…
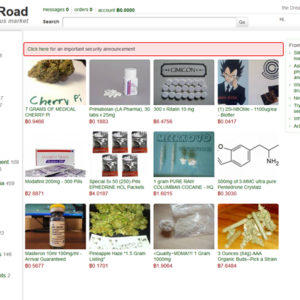
Exploring the Darkweb: Unveiling the Hidden Layers of the Internet
“Exploring the Darkweb: Unveiling the Hidden Layers of the Internet” Introduction: The internet is often referred to as the tip…
Behind the Shadows: The World of Darkweb Development
“Behind the Shadows: The World of Darkweb Development” Introduction: Beneath the surface of the Darkweb lies a thriving ecosystem of…
Endgame DDoS Filter 3: Fortifying Networks Against Devastating Attacks
“Endgame DDoS Filter 3: Fortifying Networks Against Devastating Attacks” Introduction: Distributed Denial of Service (DDoS) attacks continue to pose a…




Recent Comments